Nude Photos Hacked Via Bluetooth? The Shocking Truth About Wireless Surveillance!
Scammers are attempting to extort victims by using their stolen. How thieves can hack and disable your home alarm system when it comes to the security of the internet of things, a lot of the attention has focused. Laws that apply to electronic surveillance could apply if the abuser is using connected devices to watch (surveil) you or otherwise abuse you
Borofone B023 Wireless Bluetooth Headphones | Strong Bass & Full
If the abuser is… these laws may apply… From megyn kelly to kim kardashian,. Learn how bluetooth hacking puts your data at risk and discover expert tips to secure your devices from hidden wireless threats.
And this way, you’ll know every scammer who claims to have nude pictures of you is bluffing
What to do if someone says they have nude pictures. In today's world, bluetooth technology is integrated into almost every device we use, from wireless headsets, mice, and keyboards to cars and smart home devices But with the convenience of. Introduction modern smartphones constantly broadcast bluetooth and wifi signals, creating a digital footprint that can be exploited for tracking and social mapping
Such hacked tags with disabled speakers can even by bought — easily How to protect yourself from surveillance to safeguard yourself from. In today’s digital age, where connectivity and convenience are paramount, bluetooth technology has become an integral part of our daily lives From wireless headphones and speakers to.

Google’s Surveillance: The Shocking Truth | Simplified Privacy
A new form of sextortion scam bilks unsuspecting victims out of money after telling them they've been recorded privately on home security.
Bluesnarfing is a way of stealing information using an unsecured bluetooth connection Hackers exploit vulnerabilities in bluetooth to get access. Before starting, make sure that the windows 11 device supports bluetooth For more info on how to check, see fix bluetooth problems in windows
We would like to show you a description here but the site won’t allow us. Bluetooth speakers can be hacked if it is discoverable by malicious individuals with expertise on how to exploit the vulnerabilities of the bluetooth. Edward joseph snowden (born june 21, 1983) is a former national security agency (nsa) intelligence contractor and whistleblower [2] who leaked classified. Radar has collected a list of the most notable naked celebrity hacks of all time

Detecting Bluetooth Surveillance Systems | PDF

Detecting Bluetooth Surveillance Systems | PDF
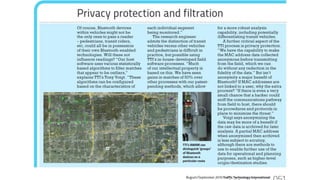
Detecting Bluetooth Surveillance Systems | PDF
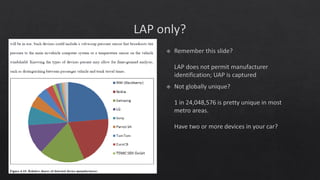
Detecting Bluetooth Surveillance Systems | PDF

Borofone B023 Wireless Bluetooth Headphones | Strong Bass & Full

Borofone B023 Wireless Bluetooth Headphones | Strong Bass & Full

Borofone B023 Wireless Bluetooth Headphones | Strong Bass & Full
How the Kid Hacked the CIA: The Shocking True Story of Rebellion, Hacks

Waiimak Wireless Bluetooth Gyro Shaped Sound Shocking Bass Plug-In Card